Some OBS Studio users may have unknowingly downloaded malware-infected plugins from the official OBS forum. And the worst part? It was going on for weeks.
OBS Studio, the free streaming and recording software used by millions of content creators and streamers worldwide, posted a security notice yesterday disclosing a coordinated attack on its forum. Hackers didn’t break into OBS itself. Instead, they quietly took over plugin developer accounts and replaced legitimate plugin files with malicious versions.
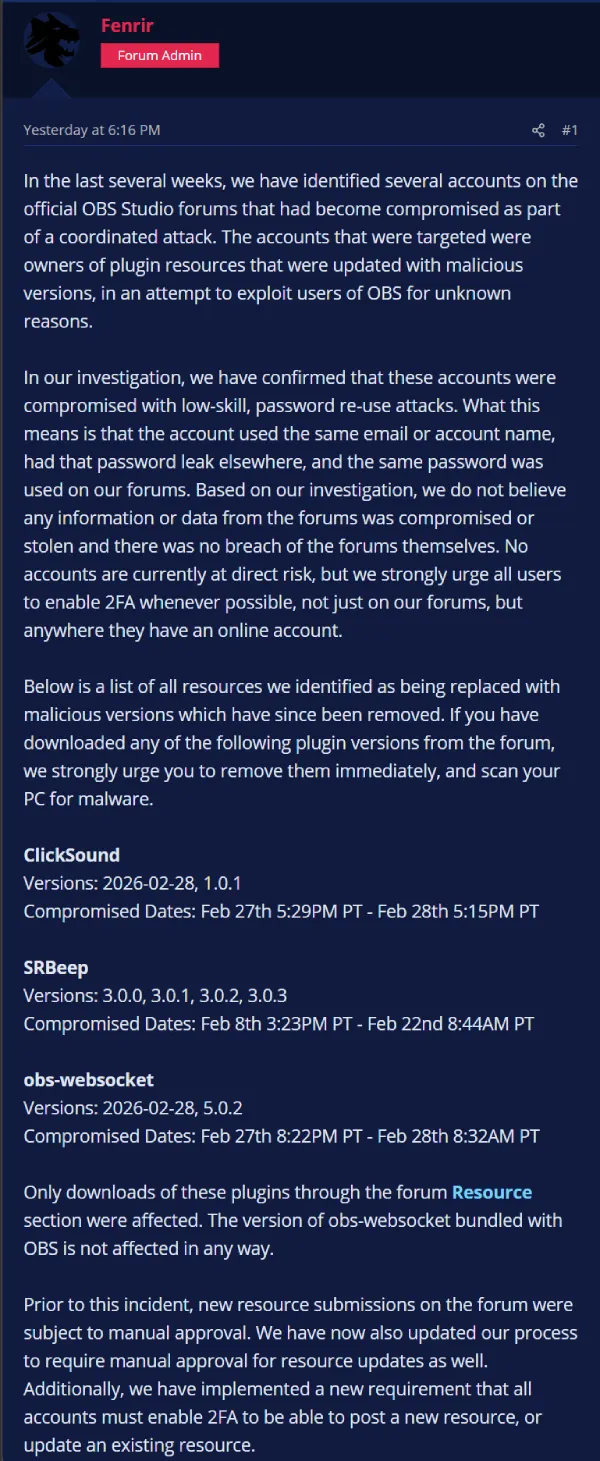
Three plugins were affected: ClickSound, SRBeep, and obs-websocket. According to the official incident report, SRBeep was compromised the longest, running from February 8 through February 22. That means some users could have had malware sitting on their machines for nearly a month before OBS caught it.
The attackers didn’t even do anything fancy to get in. They used passwords that had leaked from other breached websites and tried the same credentials on OBS forum accounts. It worked. OBS themselves called it a “low-skill, password re-use attack,” which makes it both embarrassing and a very common story in cybersecurity.
There’s still some good news though. The OBS app itself is clean. The version of obs-websocket that ships with OBS and the one on GitHub were never touched. Only downloads through the OBS forum’s Resource section were affected. For obs-websocket specifically, only about 80 downloads happened during the window it was compromised, so the actual reach there was pretty limited.
If you downloaded ClickSound (versions 2026-02-28 or 1.0.1), SRBeep (3.0.0 through 3.0.3), or obs-websocket (2026-02-28 or 5.0.2) directly from the OBS forum between late January and late February, delete them and run a full malware scan on your PC.
OBS has since pulled all the affected files. Going forward, plugin updates, not just new submissions, will now require manual approval before going live. Developers also have to enable two-factor authentication (2FA) to post or update any resource on the forum.
The incident is a good reminder that even “official” sources can get compromised, and that reusing passwords across websites is still one of the easiest ways attackers get a foot in the door. If you use the same password on multiple sites, now’s a solid time to fix that.
Featured image generated with AI
TechIssuesToday primarily focuses on publishing 'breaking' or 'exclusive' tech news. This means, we are usually the first news website on the whole Internet to highlight the topics we cover daily. So far, our stories have been picked up by many mainstream technology publications like The Verge, Macrumors, Forbes, etc. To know more, head here.