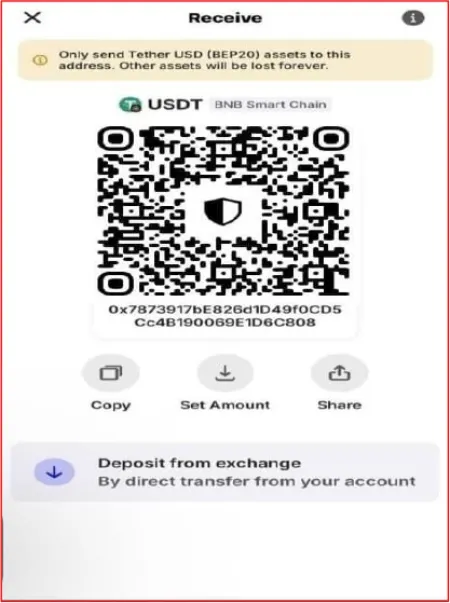
A new phishing campaign is going after Trust Wallet users, and it relies on malicious QR codes that are surprisingly effective. Scammers are pushing these codes out through Telegram groups and messages, where people might not think twice before scanning.
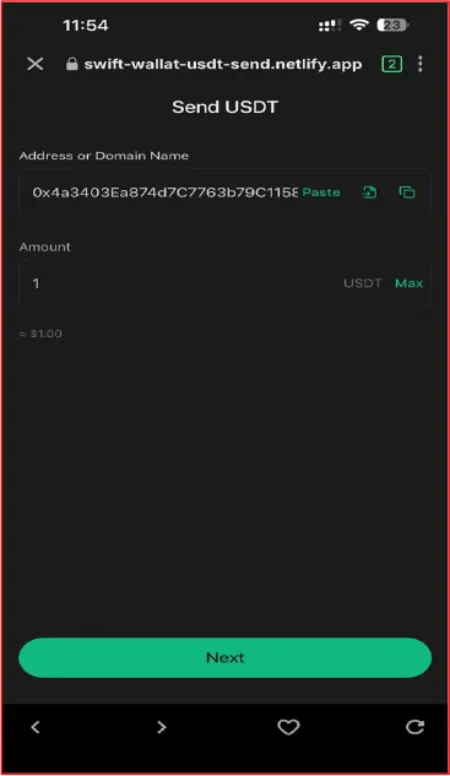
Scanning one of the codes takes you straight to a counterfeit webpage. It is built to mirror the official Trust Wallet interface for sending USDT. The page asks for a transfer amount and the address of the person receiving the funds. Everything on screen looks ordinary and familiar.
Behind the scenes though, the process is far from normal. Approving what seems like a standard transaction actually sets up unlimited access for the attackers to your USDT. They can then pull out funds from your wallet at any point without needing further confirmation from you.
According to a report released by cybersecurity company CYFIRMA on April 14, the attackers have been keeping tabs on their victims in real time. At least 52 transaction alerts came through the Telegram bot they use for monitoring. This confirms the campaign is actively targeting and succeeding against real users.
The fraudulent sites are all hosted on the Netlify platform. Some of the domains involved include things like swift-wallat-usdt-send.netlify.app and send-usdt-09-admin.netlify.app.
The QR codes are designed to first route through links that resemble official Trust Wallet pages. That extra step makes them much harder to spot as suspicious during a fast check.
The scammers chose to operate on the BNB Smart Chain for practical reasons. Transaction costs stay very low on that network, so they can afford to run the scheme on a bigger scale without spending much.
One of the more deceptive parts is how the page often presents the transaction as if it involves only about one dollar. It gives the impression of a small and harmless action. In reality, that signature grants broad, unlimited approval over the entire USDT balance held in the wallet.
These approvals do not automatically go away once you exit the fake page. They remain in effect until the user goes through the proper steps to cancel them. Anyone who has fallen for this needs to act quickly to protect what is left.
This attack follows the Drainer-as-a-Service model. One group builds the draining tools and sells or rents them to other scammers.
Trust Wallet has no actual vulnerability. The scam works purely by tricking users into signing permissions they do not understand.
If you scanned a QR code for a USDT transfer recently, check your token approvals on BscScan right away and revoke anything you do not recognize. The full CYFIRMA report has all the details, including the attacker contract addresses.
Featured image generated with AI
TechIssuesToday primarily focuses on publishing 'breaking' or 'exclusive' tech news. This means, we are usually the first news website on the whole Internet to highlight the topics we cover daily. So far, our stories have been picked up by many mainstream technology publications like The Verge, Macrumors, Forbes, etc. To know more, head here.